-
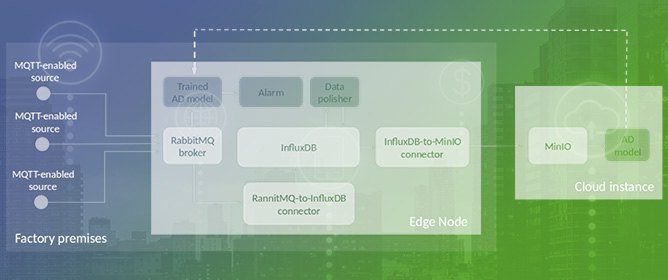 IoTwins: Implementing Distributed and Hybrid Digital Twins
IoTwins: Implementing Distributed and Hybrid Digital Twins -
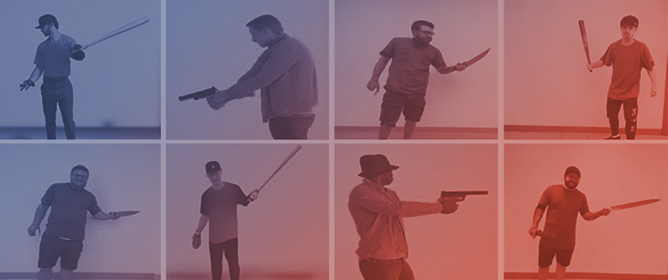 Enhancing Smart City Safety and Utilizing AI Expert Systems for Violence Detection
Enhancing Smart City Safety and Utilizing AI Expert Systems for Violence Detection -
 Proximal Policy Optimization for Efficient D2D-Assisted Computation Offloading and Resource Allocation in Multi-Access Edge Computing
Proximal Policy Optimization for Efficient D2D-Assisted Computation Offloading and Resource Allocation in Multi-Access Edge Computing -
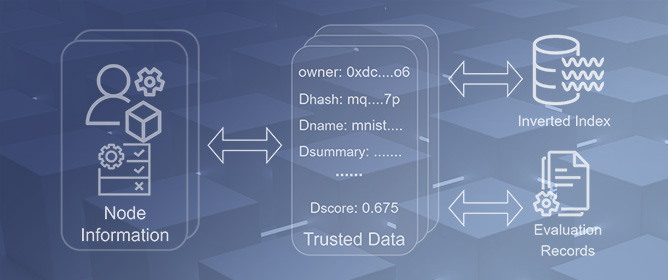 TDLearning: Trusted Distributed Collaborative Learning Based on Blockchain Smart Contracts
TDLearning: Trusted Distributed Collaborative Learning Based on Blockchain Smart Contracts
Journal Description
Future Internet
Future Internet
is an international, peer-reviewed, open access journal on internet technologies and the information society, published monthly online by MDPI.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, ESCI (Web of Science), Ei Compendex, dblp, Inspec, and other databases.
- Journal Rank: CiteScore - Q1 (Computer Networks and Communications)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 11.8 days after submission; acceptance to publication is undertaken in 2.9 days (median values for papers published in this journal in the second half of 2023).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
Impact Factor:
3.4 (2022);
5-Year Impact Factor:
3.4 (2022)
Latest Articles
A Fair Crowd-Sourced Automotive Data Monetization Approach Using Substrate Hybrid Consensus Blockchain
Future Internet 2024, 16(5), 156; https://doi.org/10.3390/fi16050156 - 30 Apr 2024
Abstract
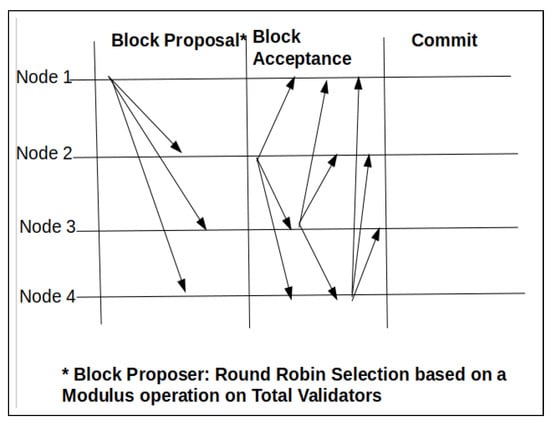
This work presents a private consortium blockchain-based automotive data monetization architecture implementation using the Substrate blockchain framework. Architecture is decentralized where crowd-sourced data from vehicles are collectively auctioned ensuring data privacy and security. Smart Contracts and OffChain worker interactions built along with the
[...] Read more.
This work presents a private consortium blockchain-based automotive data monetization architecture implementation using the Substrate blockchain framework. Architecture is decentralized where crowd-sourced data from vehicles are collectively auctioned ensuring data privacy and security. Smart Contracts and OffChain worker interactions built along with the blockchain make it interoperable with external systems to send or receive data. The work is deployed in a Kubernetes cloud platform and evaluated on different parameters like throughput, hybrid consensus algorithms AuRa and BABE, along with GRANDPA performance in terms of forks and scalability for increasing node participants. The hybrid consensus algorithms are studied in depth to understand the difference and performance in the separation of block creation by AuRa and BABE followed by chain finalization through the GRANDPA protocol.
Full article
(This article belongs to the Special Issue Security in the Internet of Things (IoT))
►
Show Figures
Open AccessArticle
Novel Approach towards a Fully Deep Learning-Based IoT Receiver Architecture: From Estimation to Decoding
by
Matthew Boeding, Michael Hempel and Hamid Sharif
Future Internet 2024, 16(5), 155; https://doi.org/10.3390/fi16050155 - 30 Apr 2024
Abstract
As the Internet of Things (IoT) continues to expand, wireless communication is increasingly widespread across diverse industries and remote devices. This includes domains such as Operational Technology in the Smart Grid. Notably, there is a surge in resource-constrained devices leveraging wireless communication, especially
[...] Read more.
As the Internet of Things (IoT) continues to expand, wireless communication is increasingly widespread across diverse industries and remote devices. This includes domains such as Operational Technology in the Smart Grid. Notably, there is a surge in resource-constrained devices leveraging wireless communication, especially with the advances of 5G/6G technology. Nevertheless, the transmission of wireless communications demands substantial power and computational resources, presenting a significant challenge to these devices and their operations. In this work, we propose the use of deep learning to improve the Bit Error Rate (BER) performance of Orthogonal Frequency Division Multiplexing (OFDM) wireless receivers. By improving the BER performance of these receivers, devices can transmit with less power, thereby improving IoT devices’ battery life. The architecture presented in this paper utilizes a depthwise Convolutional Neural Network (CNN) for channel estimation and demodulation, whereas a Graph Neural Network (GNN) is utilized for Low-Density Parity Check (LDPC) decoding, tested against a proposed (1998, 1512) LDPC code. Our results show higher performance than traditional receivers in both isolated tests for the CNN and GNN, and a combined end-to-end test with lower computational complexity than other proposed deep learning models. For BER improvement, our proposed approach showed a 1 dB improvement for eliminating BER in QPSK models. Additionally, it improved 16-QAM Rician BER by five decades, 16-QAM LOS model BER by four decades, 64-QAM Rician BER by 2.5 decades, and 64-QAM LOS model BER by three decades.
Full article
(This article belongs to the Special Issue State-of-the-Art Future Internet Technology in USA 2024–2025)
►▼
Show Figures
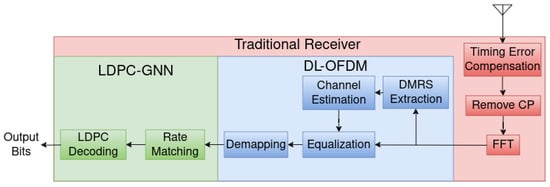
Figure 1
Open AccessArticle
A Method for the Rapid Propagation of Emergency Event Notifications in a Long Vehicle Convoy
by
John David Sprunger, Alvin Lim and David M. Bevly
Future Internet 2024, 16(5), 154; https://doi.org/10.3390/fi16050154 - 29 Apr 2024
Abstract
Convoys composed of autonomous vehicles could improve the transportation and freight industries in several ways. One of the avenues of improvement is in fuel efficiency, where the vehicles maintain a close following distance to each other in order to reduce air resistance by
[...] Read more.
Convoys composed of autonomous vehicles could improve the transportation and freight industries in several ways. One of the avenues of improvement is in fuel efficiency, where the vehicles maintain a close following distance to each other in order to reduce air resistance by way of the draft effect. While close following distances improve fuel efficiency, they also reduce both the margin of safety and the system’s tolerance to disturbances in relative position. The system’s tolerance to disturbances is known as string stability, where the error magnitude either grows or decays as it propagates rearward through the convoy. One of the major factors in a system’s string stability is its delay in sending state updates to other vehicles, the most pertinent being a hard braking maneuver. Both external sensors and vehicle-to-vehicle communication standards have relatively long delays between peer vehicle state changes and the information being actionable by the ego vehicle. The system presented here, called the Convoy Vehicular Ad Hoc Network (Convoy VANET), was designed to reliably propagate emergency event messages with low delay while maintaining reasonable channel efficiency. It accomplishes this using a combination of several techniques, notably relative position-based retransmission delays. Our results using Network Simulator 3 (ns3) show the system propagating messages down a 20-vehicle convoy in less than 100 ms even with more than a 35% message loss between vehicles that are not immediately adjacent. These simulation results show the potential for this kind of system in situations where emergency information must be disseminated quickly in low-reliability wireless environments.
Full article
(This article belongs to the Special Issue Inter-Vehicle Communication Protocols and Their Applications)
►▼
Show Figures
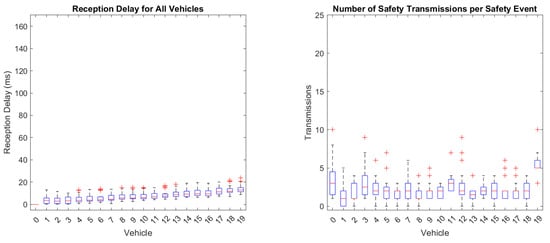
Figure 1
Open AccessArticle
A Novel Traffic Classification Approach by Employing Deep Learning on Software-Defined Networking
by
Daniel Nuñez-Agurto, Walter Fuertes, Luis Marrone, Eduardo Benavides-Astudillo, Christian Coronel-Guerrero and Franklin Perez
Future Internet 2024, 16(5), 153; https://doi.org/10.3390/fi16050153 - 29 Apr 2024
Abstract
The ever-increasing diversity of Internet applications and the rapid evolution of network infrastructure due to emerging technologies have made network management more challenging. Effective traffic classification is critical for efficiently managing network resources and aligning with service quality and security demands. The centralized
[...] Read more.
The ever-increasing diversity of Internet applications and the rapid evolution of network infrastructure due to emerging technologies have made network management more challenging. Effective traffic classification is critical for efficiently managing network resources and aligning with service quality and security demands. The centralized controller of software-defined networking provides a comprehensive network view, simplifying traffic analysis and offering direct programmability features. When combined with deep learning techniques, these characteristics enable the incorporation of intelligence into networks, leading to optimization and improved network management and maintenance. Therefore, this research aims to develop a model for traffic classification by application types and network attacks using deep learning techniques to enhance the quality of service and security in software-defined networking. The SEMMA method is employed to deploy the model, and the classifiers are trained with four algorithms, namely LSTM, BiLSTM, GRU, and BiGRU, using selected features from two public datasets. These results underscore the remarkable effectiveness of the GRU model in traffic classification. Hence, the outcomes achieved in this research surpass state-of-the-art methods and showcase the effectiveness of a deep learning model within a traffic classification in an SDN environment.
Full article
(This article belongs to the Section Smart System Infrastructure and Applications)
►▼
Show Figures
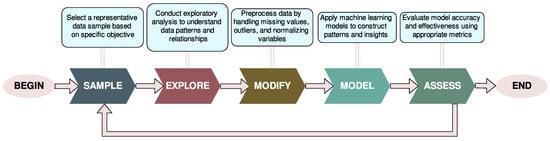
Figure 1
Open AccessArticle
A Hybrid Multi-Agent Reinforcement Learning Approach for Spectrum Sharing in Vehicular Networks
by
Mansoor Jamal, Zaib Ullah, Muddasar Naeem, Musarat Abbas and Antonio Coronato
Future Internet 2024, 16(5), 152; https://doi.org/10.3390/fi16050152 - 28 Apr 2024
Abstract
Efficient spectrum sharing is essential for maximizing data communication performance in Vehicular Networks (VNs). In this article, we propose a novel hybrid framework that leverages Multi-Agent Reinforcement Learning (MARL), thereby combining both centralized and decentralized learning approaches. This framework addresses scenarios where multiple
[...] Read more.
Efficient spectrum sharing is essential for maximizing data communication performance in Vehicular Networks (VNs). In this article, we propose a novel hybrid framework that leverages Multi-Agent Reinforcement Learning (MARL), thereby combining both centralized and decentralized learning approaches. This framework addresses scenarios where multiple vehicle-to-vehicle (V2V) links reuse the frequency spectrum preoccupied by vehicle-to-infrastructure (V2I) links. We introduce the QMIX technique with the Deep Q Networks (DQNs) algorithm to facilitate collaborative learning and efficient spectrum management. The DQN technique uses a neural network to approximate the Q value function in high-dimensional state spaces, thus mapping input states to (action, Q value) tables that facilitate self-learning across diverse scenarios. Similarly, the QMIX is a value-based technique for multi-agent environments. In the proposed model, each V2V agent having its own DQN observes the environment, receives observation, and obtains a common reward. The QMIX network receives Q values from all agents considering individual benefits and collective objectives. This mechanism leads to collective learning while V2V agents dynamically adapt to real-time conditions, thus improving VNs performance. Our research finding highlights the potential of hybrid MARL models for dynamic spectrum sharing in VNs and paves the way for advanced cooperative learning strategies in vehicular communication environments. Furthermore, we conducted an in-depth exploration of the simulation environment and performance evaluation criteria, thus concluding in a comprehensive comparative analysis with cutting-edge solutions in the field. Simulation results show that the proposed framework efficiently performs against the benchmark architecture in terms of V2V transmission probability and V2I peak data transfer.
Full article
(This article belongs to the Special Issue IoT, Edge, and Cloud Computing in Smart Cities)
►▼
Show Figures
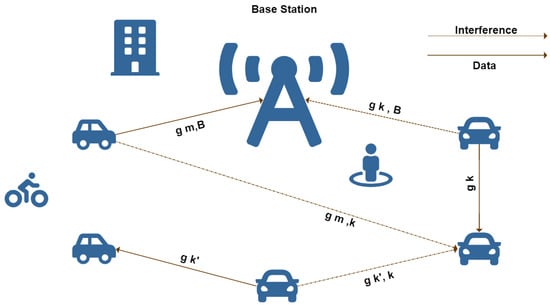
Figure 1
Open AccessArticle
Effective Monoaural Speech Separation through Convolutional Top-Down Multi-View Network
by
Aye Nyein Aung, Che-Wei Liao and Jeih-Weih Hung
Future Internet 2024, 16(5), 151; https://doi.org/10.3390/fi16050151 - 28 Apr 2024
Abstract
Speech separation, sometimes known as the “cocktail party problem”, is the process of separating individual speech signals from an audio mixture that includes ambient noises and several speakers. The goal is to extract the target speech in this complicated sound scenario and either
[...] Read more.
Speech separation, sometimes known as the “cocktail party problem”, is the process of separating individual speech signals from an audio mixture that includes ambient noises and several speakers. The goal is to extract the target speech in this complicated sound scenario and either make it easier to understand or increase its quality so that it may be used in subsequent processing. Speech separation on overlapping audio data is important for many speech-processing tasks, including natural language processing, automatic speech recognition, and intelligent personal assistants. New speech separation algorithms are often built on a deep neural network (DNN) structure, which seeks to learn the complex relationship between the speech mixture and any specific speech source of interest. DNN-based speech separation algorithms outperform conventional statistics-based methods, although they typically need a lot of processing and/or a larger model size. This study presents a new end-to-end speech separation network called ESC-MASD-Net (effective speaker separation through convolutional multi-view attention and SuDoRM-RF network), which has relatively fewer model parameters compared with the state-of-the-art speech separation architectures. The network is partly inspired by the SuDoRM-RF++ network, which uses multiple time-resolution features with downsampling and resampling for effective speech separation. ESC-MASD-Net incorporates the multi-view attention and residual conformer modules into SuDoRM-RF++. Additionally, the U-Convolutional block in ESC-MASD-Net is refined with a conformer layer. Experiments conducted on the WHAM! dataset show that ESC-MASD-Net outperforms SuDoRM-RF++ significantly in the SI-SDRi metric. Furthermore, the use of the conformer layer has also improved the performance of ESC-MASD-Net.
Full article
(This article belongs to the Special Issue AI and Security in 5G Cooperative Cognitive Radio Networks)
►▼
Show Figures
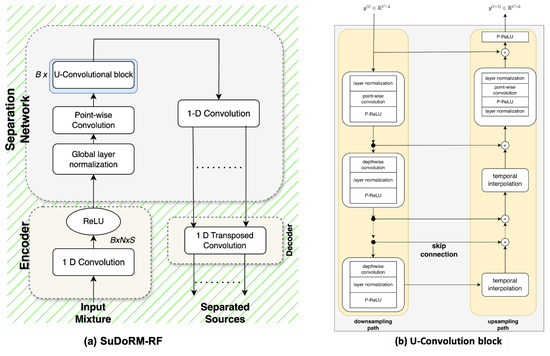
Figure 1
Open AccessArticle
Exploring Data Input Problems in Mixed Reality Environments: Proposal and Evaluation of Natural Interaction Techniques
by
Jingzhe Zhang, Tiange Chen, Wenjie Gong, Jiayue Liu and Jiangjie Chen
Future Internet 2024, 16(5), 150; https://doi.org/10.3390/fi16050150 - 27 Apr 2024
Abstract
Data input within mixed reality environments poses significant interaction challenges, notably in immersive visual analytics applications. This study assesses five numerical input techniques: three benchmark methods (Touch-Slider, Keyboard, Pinch-Slider) and two innovative multimodal techniques (Bimanual Scaling, Gesture and Voice). An experimental design was
[...] Read more.
Data input within mixed reality environments poses significant interaction challenges, notably in immersive visual analytics applications. This study assesses five numerical input techniques: three benchmark methods (Touch-Slider, Keyboard, Pinch-Slider) and two innovative multimodal techniques (Bimanual Scaling, Gesture and Voice). An experimental design was employed to compare these techniques’ input efficiency, accuracy, and user experience across varying precision and distance conditions. The findings reveal that multimodal techniques surpass slider methods in input efficiency yet are comparable to keyboards; the voice method excels in reducing cognitive load but falls short in accuracy; and the scaling method marginally leads in user satisfaction but imposes a higher physical load. Furthermore, this study outlines these techniques’ pros and cons and offers design guidelines and future research directions.
Full article
(This article belongs to the Special Issue Novel Advances in Collaborative Environments for Virtual, Augmented, Mixed and Extended Reality)
►▼
Show Figures
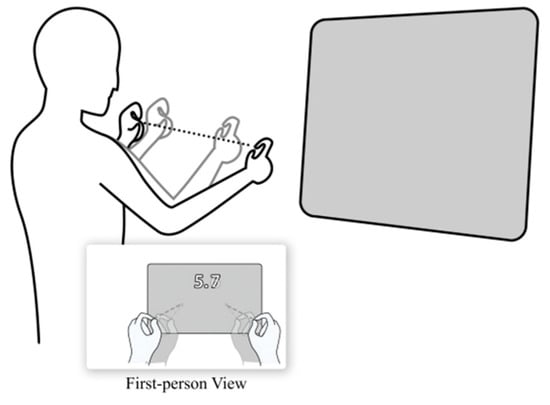
Figure 1
Open AccessArticle
A Blockchain-Based Real-Time Power Balancing Service for Trustless Renewable Energy Grids
by
Andrea Calvagna, Giovanni Marotta, Giuseppe Pappalardo and Emiliano Tramontana
Future Internet 2024, 16(5), 149; https://doi.org/10.3390/fi16050149 - 26 Apr 2024
Abstract
We face a decentralized renewable energy production scenario, where a large number of small energy producers, i.e., prosumers, contribute to a common distributor entity, who resells energy directly to end-users. A major challenge for the distributor is to ensure power stability, constantly balancing
[...] Read more.
We face a decentralized renewable energy production scenario, where a large number of small energy producers, i.e., prosumers, contribute to a common distributor entity, who resells energy directly to end-users. A major challenge for the distributor is to ensure power stability, constantly balancing produced vs consumed energy flows. In this context, being able to provide quick restore actions in response to unpredictable unbalancing events is a must, as fluctuations are the norm for renewable energy sources. To this aim, the high scalability and diversity of sources are crucial requirements for the said balancing to be actually manageable. In this study, we explored the challenges and benefits of adopting a blockchain-based software architecture as a scalable, trustless interaction platform between prosumers’ smart energy meters and the distributor. Our developed prototype accomplishes the energy load balancing service via smart contracts deployed in a real blockchain network with an increasing number of simulated prosumers. We show that the blockchain-based application managed to react in a timely manner to energy unbalances for up to a few hundred prosumers.
Full article
(This article belongs to the Special Issue Blockchain and Artificial Intelligence for Decentralized Edge Environments)
►▼
Show Figures

Figure 1
Open AccessArticle
HSM4SSL: Leveraging HSMs for Enhanced Intra-Domain Security
by
Yazan Aref and Abdelkader Ouda
Future Internet 2024, 16(5), 148; https://doi.org/10.3390/fi16050148 - 26 Apr 2024
Abstract
In a world where digitization is rapidly advancing, the security and privacy of intra-domain communication within organizations are of critical concern. The imperative to secure communication channels among physical systems has led to the deployment of various security approaches aimed at fortifying networking
[...] Read more.
In a world where digitization is rapidly advancing, the security and privacy of intra-domain communication within organizations are of critical concern. The imperative to secure communication channels among physical systems has led to the deployment of various security approaches aimed at fortifying networking protocols. However, these approaches have typically been designed to secure protocols individually, lacking a holistic perspective on the broader challenge of intra-domain communication security. This omission raises fundamental concerns about the safety and integrity of intra-domain environments, where all communication occurs within a single domain. As a result, this paper introduces HSM4SSL, a comprehensive solution designed to address the evolving challenges of secure data transmission in intra-domain environments. By leveraging hardware security modules (HSMs), HSM4SSL aims to utilize the Secure Socket Layer (SSL) protocol within intra-domain environments to ensure data confidentiality, authentication, and integrity. In addition, solutions proposed by academic researchers and in the industry have not addressed the issue in a holistic and integrative manner, as they only apply to specific types of environments or servers and do not utilize all cryptographic operations for robust security. Thus, HSM4SSL bridges this gap by offering a unified and comprehensive solution that includes certificate management, key management practices, and various security services. HSM4SSL comprises three layers to provide a standardized interaction between software applications and HSMs. A performance evaluation was conducted comparing HSM4SSL with a benchmark tool for cryptographic operations. The results indicate that HSM4SSL achieved 33% higher requests per second (RPS) compared to OpenSSL, along with a 13% lower latency rate. Additionally, HSM4SSL efficiently utilizes CPU and network resources, outperforming OpenSSL in various aspects. These findings highlight the effectiveness and reliability of HSM4SSL in providing secure communication within intra-domain environments, thus addressing the pressing need for enhanced security mechanisms.
Full article
(This article belongs to the Special Issue Security and Privacy in Blockchains and the IoT III)
►▼
Show Figures
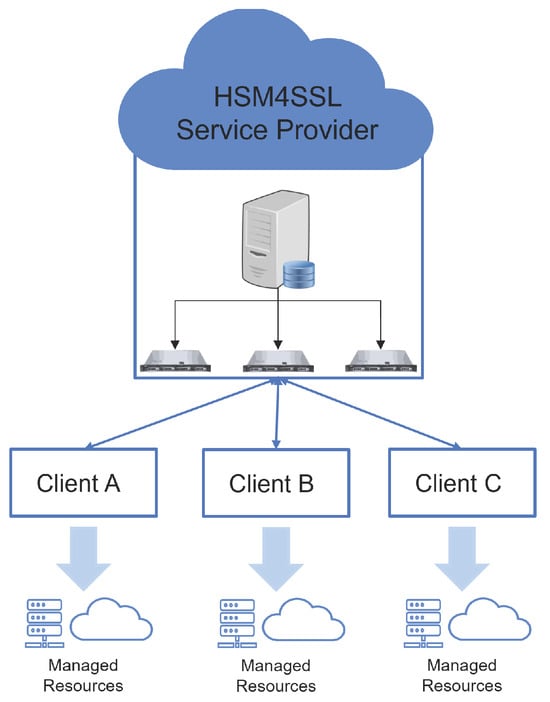
Figure 1
Open AccessArticle
A New Generation of Collaborative Immersive Analytics on the Web: Open-Source Services to Capture, Process and Inspect Users’ Sessions in 3D Environments
by
Bruno Fanini and Giorgio Gosti
Future Internet 2024, 16(5), 147; https://doi.org/10.3390/fi16050147 - 25 Apr 2024
Abstract
Recording large amounts of users’ sessions performed through 3D applications may provide crucial insights into interaction patterns. Such data can be captured from interactive experiences in public exhibits, remote motion tracking equipment, immersive XR devices, lab installations or online web applications. Immersive analytics
[...] Read more.
Recording large amounts of users’ sessions performed through 3D applications may provide crucial insights into interaction patterns. Such data can be captured from interactive experiences in public exhibits, remote motion tracking equipment, immersive XR devices, lab installations or online web applications. Immersive analytics (IA) deals with the benefits and challenges of using immersive environments for data analysis and related design solutions to improve the quality and efficiency of the analysis process. Today, web technologies allow us to craft complex applications accessible through common browsers, and APIs like WebXR allow us to interact with and explore virtual 3D environments using immersive devices. These technologies can be used to access rich, immersive spaces but present new challenges related to performance, network bottlenecks and interface design. WebXR IA tools are still quite new in the literature: they present several challenges and leave quite unexplored the possibility of synchronous collaborative inspection. The opportunity to share the virtual space with remote analysts in fact improves sense-making tasks and offers new ways to discuss interaction patterns together, while inspecting captured records or data aggregates. Furthermore, with proper collaborative approaches, analysts are able to share machine learning (ML) pipelines and constructively discuss the outcomes and insights through tailored data visualization, directly inside immersive 3D spaces, using a web browser. Under the H2IOSC project, we present the first results of an open-source pipeline involving tools and services aimed at capturing, processing and inspecting interactive sessions collaboratively in WebXR with other analysts. The modular pipeline can be easily deployed in research infrastructures (RIs), remote dedicated hubs or local scenarios. The developed WebXR immersive analytics tool specifically offers advanced features for volumetric data inspection, query, annotation and discovery, alongside spatial interfaces. We assess the pipeline through users’ sessions captured during two remote public exhibits, by a WebXR application presenting generative AI content to visitors. We deployed the pipeline to assess the different services and to better understand how people interact with generative AI environments. The obtained results can be easily adopted for a multitude of case studies, interactive applications, remote equipment or online applications, to support or accelerate the detection of interaction patterns among remote analysts collaborating in the same 3D space.
Full article
(This article belongs to the Special Issue Novel Advances in Collaborative Environments for Virtual, Augmented, Mixed and Extended Reality)
►▼
Show Figures
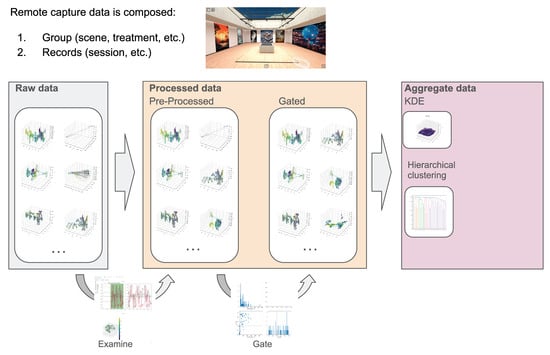
Figure 1
Open AccessArticle
Median Absolute Deviation for BGP Anomaly Detection
by
Maria Andrea Romo-Chavero, Jose Antonio Cantoral-Ceballos, Jesus Arturo Pérez-Díaz and Carlos Martinez-Cagnazzo
Future Internet 2024, 16(5), 146; https://doi.org/10.3390/fi16050146 - 25 Apr 2024
Abstract
The stability and reliability of the global Internet infrastructure heavily rely on the Border Gateway Protocol (BGP), a crucial protocol that facilitates the exchange of routing information among various Autonomous Systems, ensuring seamless connectivity worldwide. However, BGP inherently possesses a susceptibility to abnormal
[...] Read more.
The stability and reliability of the global Internet infrastructure heavily rely on the Border Gateway Protocol (BGP), a crucial protocol that facilitates the exchange of routing information among various Autonomous Systems, ensuring seamless connectivity worldwide. However, BGP inherently possesses a susceptibility to abnormal routing behaviors, potentially leading to significant connectivity disruptions. Despite extensive efforts, accurately detecting and effectively mitigating such abnormalities persist as tough challenges. To tackle these, this article proposes a novel statistical approach employing the median absolute deviation under certain constraints to proactively detect anomalies in BGP. By applying advanced analysis techniques, this research offers a robust method for the early detection of anomalies, such as Internet worms, configuration errors, and link failures. This innovative approach has been empirically validated, achieving an accuracy rate of 90% and a precision of 95% in identifying these disruptions. This high level of precision and accuracy not only confirms the effectiveness of the statistical method employed but also marks a significant step forward for enhancing the stability and reliability of the global Internet infrastructure.
Full article
(This article belongs to the Special Issue Information and Future Internet Security, Trust and Privacy II)
►▼
Show Figures
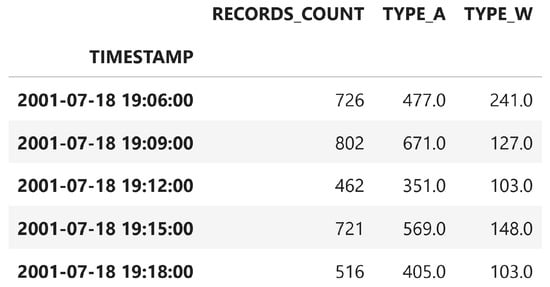
Figure 1
Open AccessArticle
Design and Implementation of a Low-Cost, Linear Robotic Camera System, Targeting Greenhouse Plant Growth Monitoring
by
Zacharias Kamarianakis, Spyros Perdikakis, Ioannis N. Daliakopoulos, Dimitrios M. Papadimitriou and Spyros Panagiotakis
Future Internet 2024, 16(5), 145; https://doi.org/10.3390/fi16050145 - 23 Apr 2024
Abstract
Automated greenhouse production systems frequently employ non-destructive techniques, such as computer vision-based methods, to accurately measure plant physiological properties and monitor crop growth. By utilizing an automated image acquisition and analysis system, it becomes possible to swiftly assess the growth and health of
[...] Read more.
Automated greenhouse production systems frequently employ non-destructive techniques, such as computer vision-based methods, to accurately measure plant physiological properties and monitor crop growth. By utilizing an automated image acquisition and analysis system, it becomes possible to swiftly assess the growth and health of plants throughout their entire lifecycle. This valuable information can be utilized by growers, farmers, and crop researchers who are interested in self-cultivation procedures. At the same time, such a system can alleviate the burden of daily plant photography for human photographers and crop researchers, while facilitating automated plant image acquisition for crop status monitoring. Given these considerations, the aim of this study was to develop an experimental, low-cost, 1-DOF linear robotic camera system specifically designed for automated plant photography. As an initial evaluation of the proposed system, which targets future research endeavors of simplifying the process of plant growth monitoring in a small greenhouse, the experimental setup and precise plant identification and localization are demonstrated in this work through an application on lettuce plants, imaged mostly under laboratory conditions.
Full article
(This article belongs to the Section Smart System Infrastructure and Applications)
►▼
Show Figures
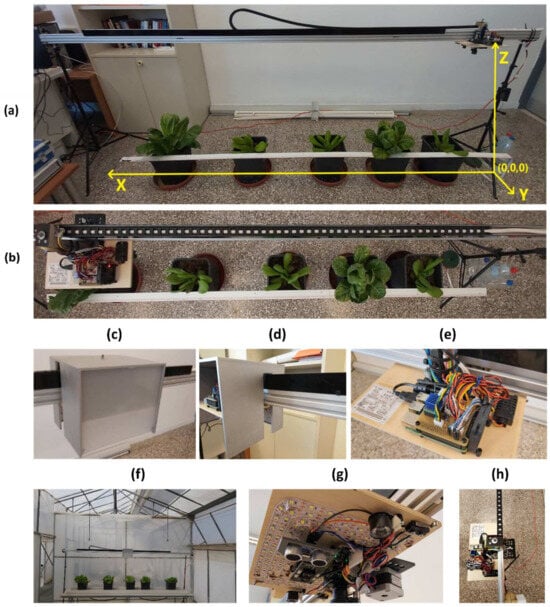
Figure 1
Open AccessArticle
Anticipating Job Market Demands—A Deep Learning Approach to Determining the Future Readiness of Professional Skills
by
Albert Weichselbraun, Norman Süsstrunk, Roger Waldvogel, André Glatzl, Adrian M. P. Braşoveanu and Arno Scharl
Future Internet 2024, 16(5), 144; https://doi.org/10.3390/fi16050144 - 23 Apr 2024
Abstract
Anticipating the demand for professional job market skills needs to consider trends such as automation, offshoring, and the emerging Gig economy, as they significantly impact the future readiness of skills. This article draws on the scientific literature, expert assessments, and deep learning to
[...] Read more.
Anticipating the demand for professional job market skills needs to consider trends such as automation, offshoring, and the emerging Gig economy, as they significantly impact the future readiness of skills. This article draws on the scientific literature, expert assessments, and deep learning to estimate two indicators of high relevance for a skill’s future readiness: its automatability and offshorability. Based on gold standard data, we evaluate the performance of Support Vector Machines (SVMs), Transformers, Large Language Models (LLMs), and a deep learning ensemble classifier for propagating expert and literature assessments on these indicators of yet unseen skills. The presented approach uses short bipartite skill labels that contain a skill topic (e.g., “Java”) and a corresponding verb (e.g., “programming”) to describe the skill. Classifiers thus need to base their judgments solely on these two input terms. Comprehensive experiments on skewed and balanced datasets show that, in this low-token setting, classifiers benefit from pre-training and fine-tuning and that increased classifier complexity does not yield further improvements.
Full article
(This article belongs to the Collection Innovative People-Centered Solutions Applied to Industries, Cities and Societies)
►▼
Show Figures

Graphical abstract
Open AccessArticle
Multi-Constraint and Multi-Policy Path Hopping Active Defense Method Based on SDN
by
Bing Zhang, Hui Li, Shuai Zhang, Jing Sun, Ning Wei, Wenhong Xu and Huan Wang
Future Internet 2024, 16(4), 143; https://doi.org/10.3390/fi16040143 - 22 Apr 2024
Abstract
Path hopping serves as an active defense mechanism in network security, yet it encounters challenges like a restricted path switching space, the recurrent use of similar paths and vital nodes, a singular triggering mechanism for path switching, and fixed hopping intervals. This paper
[...] Read more.
Path hopping serves as an active defense mechanism in network security, yet it encounters challenges like a restricted path switching space, the recurrent use of similar paths and vital nodes, a singular triggering mechanism for path switching, and fixed hopping intervals. This paper introduces an active defense method employing multiple constraints and strategies for path hopping. A depth-first search (DFS) traversal is utilized to compute all possible paths between nodes, thereby broadening the path switching space while simplifying path generation complexity. Subsequently, constraints are imposed on residual bandwidth, selection periods, path similitude, and critical nodes to reduce the likelihood of reusing similar paths and crucial nodes. Moreover, two path switching strategies are formulated based on the weights of residual bandwidth and critical nodes, along with the calculation of path switching periods. This facilitates adaptive switching of path hopping paths and intervals, contingent on the network’s residual bandwidth threshold, in response to diverse attack scenarios. Simulation outcomes illustrate that this method, while maintaining normal communication performance, expands the path switching space effectively, safeguards against eavesdropping and link-flooding attacks, enhances path switching diversity and unpredictability, and fortifies the network’s resilience against malicious attacks.
Full article
(This article belongs to the Special Issue Information and Future Internet Security, Trust and Privacy II)
►▼
Show Figures
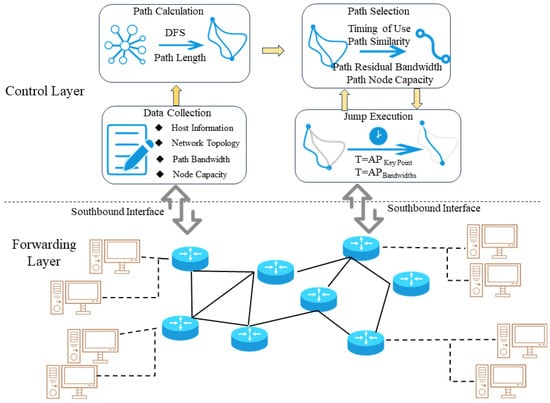
Figure 1
Open AccessArticle
Edge Federated Optimization for Heterogeneous Data
by
Hsin-Tung Lin and Chih-Yu Wen
Future Internet 2024, 16(4), 142; https://doi.org/10.3390/fi16040142 - 22 Apr 2024
Abstract
This study focuses on optimizing federated learning in heterogeneous data environments. We implement the FedProx and a baseline algorithm (i.e., the FedAvg) with advanced optimization strategies to tackle non-IID data issues in distributed learning. Model freezing and pruning techniques are explored to showcase
[...] Read more.
This study focuses on optimizing federated learning in heterogeneous data environments. We implement the FedProx and a baseline algorithm (i.e., the FedAvg) with advanced optimization strategies to tackle non-IID data issues in distributed learning. Model freezing and pruning techniques are explored to showcase the effective operations of deep learning models on resource-constrained edge devices. Experimental results show that at a pruning rate of 10%, the FedProx with structured pruning in the MIT-BIH and ST databases achieved the best F1 scores, reaching 96.01% and 77.81%, respectively, which achieves a good balance between system efficiency and model accuracy compared to those of the FedProx with the original configuration, reaching F1 scores of 66.12% and 89.90%, respectively. Similarly, with layer freezing technique, unstructured pruning method, and a pruning rate of 20%, the FedAvg algorithm effectively balances classification performance and degradation of pruned model accuracy, achieving F1 scores of 88.75% and 72.75%, respectively, compared to those of the FedAvg with the original configuration, reaching 56.82% and 85.80%, respectively. By adopting model optimization strategies, a practical solution is developed for deploying complex models in edge federated learning, vital for its efficient implementation.
Full article
(This article belongs to the Special Issue Software-Driven Federated Learning for/in Smart Environment)
►▼
Show Figures

Figure 1
Open AccessCorrection
Correction: Li et al. A Learning Game-Based Approach to Task-Dependent Edge Resource Allocation. Future Internet 2023, 15, 395
by
Zuopeng Li, Hengshuai Ju and Zepeng Ren
Future Internet 2024, 16(4), 141; https://doi.org/10.3390/fi16040141 - 22 Apr 2024
Abstract
In the original publication [...]
Full article
(This article belongs to the Section Internet of Things)
Open AccessArticle
SUDC: Synchronous Update with the Division and Combination of SRv6 Policy
by
Yuze Liu, Weihong Wu, Ying Wang, Jiang Liu and Fan Yang
Future Internet 2024, 16(4), 140; https://doi.org/10.3390/fi16040140 - 22 Apr 2024
Abstract
►▼
Show Figures
With the expansion of network scale, new network services are emerging. Segment Routing over IPv6 (SRv6) can meet the diverse needs of more new services due to its excellent scalability and programmability. In the intelligent 6-Generation (6G) scenario, frequent SRv6 Traffic Engineering (TE)
[...] Read more.
With the expansion of network scale, new network services are emerging. Segment Routing over IPv6 (SRv6) can meet the diverse needs of more new services due to its excellent scalability and programmability. In the intelligent 6-Generation (6G) scenario, frequent SRv6 Traffic Engineering (TE) policy updates will result in the serious problem of unsynchronized updates across routers. Existing solutions suffer from issues such as long update cycles or large data overhead. To optimize the policy-update process, this paper proposes a scheme called Synchronous Update with the Division and Combination of SRv6 Policy (SUDC). Based on the characteristics of the SRv6 TE policy, SUDC divides the policies and introduces Bit Index Explicit Replication IPv6 Encapsulation (BIERv6) to multicast the policy blocks derived from policy dividing. The contribution of this paper is to propose the policy-dividing and combination mechanism and the policy-dividing algorithm. The simulation results demonstrate that compared with the existing schemes, the update overhead and update cycle of SUDC are reduced by 46.71% and 46.6%, respectively. The problem of unsynchronized updates across routers has been further improved.
Full article
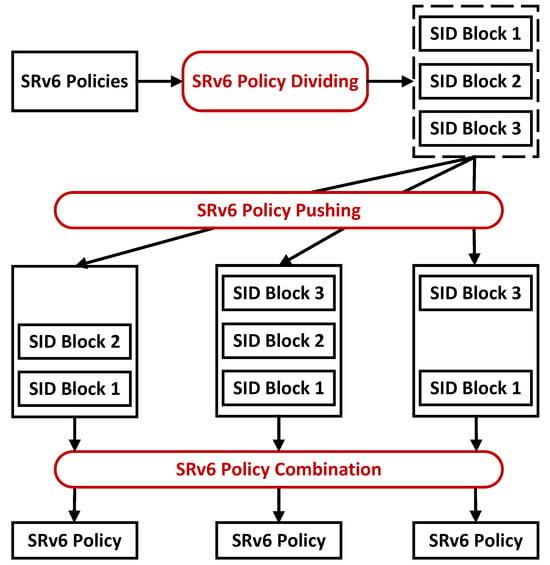
Figure 1
Open AccessReview
A Comprehensive Review of Machine Learning Approaches for Anomaly Detection in Smart Homes: Experimental Analysis and Future Directions
by
Md Motiur Rahman, Deepti Gupta, Smriti Bhatt, Shiva Shokouhmand and Miad Faezipour
Future Internet 2024, 16(4), 139; https://doi.org/10.3390/fi16040139 - 19 Apr 2024
Abstract
Detecting anomalies in human activities is increasingly crucial today, particularly in nuclear family settings, where there may not be constant monitoring of individuals’ health, especially the elderly, during critical periods. Early anomaly detection can prevent from attack scenarios and life-threatening situations. This task
[...] Read more.
Detecting anomalies in human activities is increasingly crucial today, particularly in nuclear family settings, where there may not be constant monitoring of individuals’ health, especially the elderly, during critical periods. Early anomaly detection can prevent from attack scenarios and life-threatening situations. This task becomes notably more complex when multiple ambient sensors are deployed in homes with multiple residents, as opposed to single-resident environments. Additionally, the availability of datasets containing anomalies representing the full spectrum of abnormalities is limited. In our experimental study, we employed eight widely used machine learning and two deep learning classifiers to identify anomalies in human activities. We meticulously generated anomalies, considering all conceivable scenarios. Our findings reveal that the Gated Recurrent Unit (GRU) excels in accurately classifying normal and anomalous activities, while the naïve Bayes classifier demonstrates relatively poor performance among the ten classifiers considered. We conducted various experiments to assess the impact of different training–test splitting ratios, along with a five-fold cross-validation technique, on the performance. Notably, the GRU model consistently outperformed all other classifiers under both conditions. Furthermore, we offer insights into the computational costs associated with these classifiers, encompassing training and prediction phases. Extensive ablation experiments conducted in this study underscore that all these classifiers can effectively be deployed for anomaly detection in two-resident homes.
Full article
(This article belongs to the Special Issue Machine Learning for Blockchain and IoT Systems in Smart City)
►▼
Show Figures

Graphical abstract
Open AccessArticle
SRv6-Based Edge Service Continuity in 5G Mobile Networks
by
Laura Lemmi, Carlo Puliafito, Antonio Virdis and Enzo Mingozzi
Future Internet 2024, 16(4), 138; https://doi.org/10.3390/fi16040138 - 19 Apr 2024
Abstract
Ensuring compliance with the stringent latency requirements of edge services requires close cooperation between the network and computing components. Within mobile 5G networks, the nomadic behavior of users may impact the performance of edge services, prompting the need for workload migration techniques. These
[...] Read more.
Ensuring compliance with the stringent latency requirements of edge services requires close cooperation between the network and computing components. Within mobile 5G networks, the nomadic behavior of users may impact the performance of edge services, prompting the need for workload migration techniques. These techniques allow services to follow users by moving between edge nodes. This paper introduces an innovative approach for edge service continuity by integrating Segment Routing over IPv6 (SRv6) into the 5G core data plane alongside the ETSI multi-access edge computing (MEC) architecture. Our approach maintains compatibility with non-SRv6 5G network components. We use SRv6 for packet steering and Software-Defined Networking (SDN) for dynamic network configuration. Leveraging the SRv6 Network Programming paradigm, we achieve lossless workload migration by implementing a packet buffer as a virtual network function. Our buffer may be dynamically allocated and configured within the network. We test our proposed solution on a small-scale testbed consisting of an Open Network Operating System (ONOS) SDN controller and a core network made of P4 BMv2 switches, emulated using Mininet. A comparison with a non-SRv6 alternative that uses IPv6 routing shows the higher scalability and flexibility of our approach in terms of the number of rules to be installed and time required for configuration.
Full article
(This article belongs to the Special Issue Edge Intelligence: Edge Computing for 5G and the Internet of Things)
►▼
Show Figures
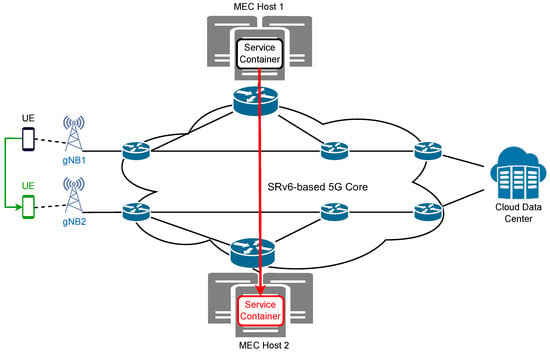
Figure 1
Open AccessArticle
From Seek-and-Destroy to Split-and-Destroy: Connection Partitioning as an Effective Tool against Low-Rate DoS Attacks
by
Vyron Kampourakis, Georgios Michail Makrakis and Constantinos Kolias
Future Internet 2024, 16(4), 137; https://doi.org/10.3390/fi16040137 - 19 Apr 2024
Abstract
Low-rate Denial of Service (LDoS) attacks are today considered one of the biggest threats against modern data centers and industrial infrastructures. Unlike traditional Distributed Denial of Service (DDoS) attacks that are mainly volumetric, LDoS attacks exhibit a very small network footprint, and therefore
[...] Read more.
Low-rate Denial of Service (LDoS) attacks are today considered one of the biggest threats against modern data centers and industrial infrastructures. Unlike traditional Distributed Denial of Service (DDoS) attacks that are mainly volumetric, LDoS attacks exhibit a very small network footprint, and therefore can easily elude standard detection and defense mechanisms. This work introduces a defense strategy that may prove particularly effective against attacks that are based on long-lived connections, an inherent trait of LDoS attacks. Our approach is based on iteratively partitioning the active connections of a victim server across a number of replica servers, and then re-evaluating the health status of each replica instance. At its core, this approach relies on live migration and containerization technologies. The main advantage of the proposed approach is that it can discover and isolate malicious connections with virtually no information about the type and characteristics of the performed attack. Additionally, while the defense takes place, there is little to no indication of the fact to the attacker. We assess various rudimentary schemes to quantify the scalability of our approach. The results from the simulations indicate that it is possible to save the vast majority of the benign connections (80%) in less than 5 min.
Full article
(This article belongs to the Section Cybersecurity)
►▼
Show Figures
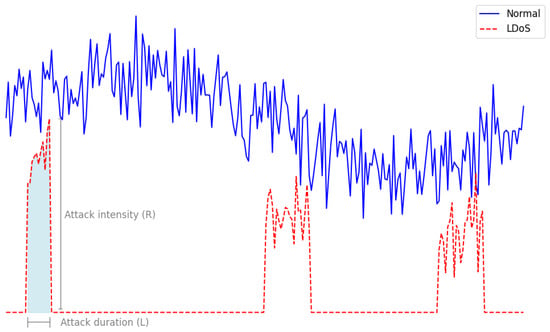
Figure 1

Journal Menu
► ▼ Journal Menu-
- Future Internet Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Instructions for Authors
- Special Issues
- Topics
- Sections & Collections
- Article Processing Charge
- Indexing & Archiving
- Editor’s Choice Articles
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Conferences
- Editorial Office
Journal Browser
► ▼ Journal BrowserHighly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Drones, Electronics, Future Internet, Information, Mathematics
Future Internet Architecture: Difficulties and Opportunities
Topic Editors: Peiying Zhang, Haotong Cao, Keping YuDeadline: 30 June 2024
Topic in
Algorithms, Future Internet, Information, Mathematics, Symmetry
Research on Data Mining of Electronic Health Records Using Deep Learning Methods
Topic Editors: Dawei Yang, Yu Zhu, Hongyi XinDeadline: 31 August 2024
Topic in
Algorithms, Axioms, Future Internet, Mathematics, Symmetry
Multimodal Sentiment Analysis Based on Deep Learning Methods Such as Convolutional Neural Networks
Topic Editors: Junaid Baber, Ali Shariq Imran, Sher Doudpota, Maheen BakhtyarDeadline: 31 October 2024
Topic in
Entropy, Future Internet, Healthcare, MAKE, Sensors
Communications Challenges in Health and Well-Being
Topic Editors: Dragana Bajic, Konstantinos Katzis, Gordana GardasevicDeadline: 20 November 2024

Conferences
Special Issues
Special Issue in
Future Internet
QoS in Wireless Sensor Network for IoT Applications
Guest Editor: Pascal LorenzDeadline: 25 May 2024
Special Issue in
Future Internet
Semantic and Social Internet of Things
Guest Editors: Konstantinos Kotis, Christos GoumopoulosDeadline: 31 May 2024
Special Issue in
Future Internet
Smart Sensorics and Robotics for IoT- and AI-Empowered Monitoring and Communication
Guest Editors: Zhongliang Zhao, Dmitry KorzunDeadline: 20 June 2024
Special Issue in
Future Internet
Machine Learning for Blockchain and IoT System in Smart Cities
Guest Editors: José A. Afonso, Joao FerreiraDeadline: 30 June 2024
Topical Collections
Topical Collection in
Future Internet
Featured Reviews of Future Internet Research
Collection Editor: Dino Giuli
Topical Collection in
Future Internet
5G/6G Networks for the Internet of Things: Communication Technologies and Challenges
Collection Editor: Sachin Sharma
Topical Collection in
Future Internet
Computer Vision, Deep Learning and Machine Learning with Applications
Collection Editors: Remus Bard, Arpad Gellert
Topical Collection in
Future Internet
Innovative People-Centered Solutions Applied to Industries, Cities and Societies
Collection Editors: Dino Giuli, Filipe Portela